Most developers assume decentralized apps are immune to security breaches because they run on blockchain, yet over $70 million was drained from Curve Finance in 2023 due to a single vulnerability. This misconception reveals a critical gap in understanding how dapps truly operate. Decentralized applications combine smart contracts with frontend interfaces, but their development demands careful attention to security, governance, and scalability challenges that differ fundamentally from traditional software. This guide breaks down the core components of dapps, explores common pitfalls, and provides actionable strategies to help you build robust blockchain applications that deliver genuine business value.
Table of Contents
- What Is A Decentralized App (Dapp)?
- Key Components And Architecture Of Decentralized Apps
- Common Security Challenges And Risks In Dapp Development
- Governance And Human Factors In Decentralized Applications
- Scalability, Testing, And Best Practices For Building Successful Dapps
- Explore Expert Blockchain Development Services
- Frequently Asked Questions
Key takeaways
| Point | Details |
|---|---|
| Dapp architecture | Decentralized apps combine immutable smart contracts as backend logic with user-facing frontends, all powered by blockchain networks that eliminate central control points. |
| Security requires vigilance | Smart contract immutability means bugs become permanent vulnerabilities, and both backend and frontend layers need rigorous testing and auditing before deployment. |
| Governance balances code and humans | Pure algorithmic governance often falls short due to rigidity, requiring community input and leadership to handle unforeseen circumstances effectively. |
| Scalability planning is essential | Applications performing well on testnets frequently struggle in production environments due to network load, demanding careful capacity planning from day one. |
What is a decentralized app (dapp)?
A decentralized application (dapp) is an application built on a decentralized network that combines a smart contract and a frontend user interface. Unlike traditional apps that rely on centralized servers controlled by a single entity, dapps operate on open public platforms like Ethereum where no single person or group holds authority over the entire system. The smart contract functions as the backend logic, executing predetermined rules automatically when specific conditions are met. This code lives permanently on the blockchain, processing transactions and managing application state without requiring a central authority to oversee operations.
The frontend interface serves as the user-facing layer, allowing people to interact with the underlying smart contracts through familiar web or mobile interfaces. This separation creates a unique architecture where business logic remains transparent and immutable on the blockchain while the presentation layer can be updated and improved over time. Decentralization removes single points of failure and censorship, distributing control across thousands of network nodes that validate and record every transaction. When you deploy a smart contract, you're essentially publishing executable code that anyone can verify and interact with according to its programmed rules.
Key characteristics that define dapps include:
- Open source code that anyone can inspect and verify
- Decentralized storage of data and application logic on blockchain networks
- Cryptographic tokens that incentivize validators and users
- Consensus mechanisms that ensure agreement across network participants without central coordination
This architecture creates applications that resist censorship, operate continuously without downtime, and execute transactions according to transparent rules that no single party can arbitrarily change. The blockchain network underpinning these applications maintains a distributed ledger that records every state change, creating an auditable history of all operations.
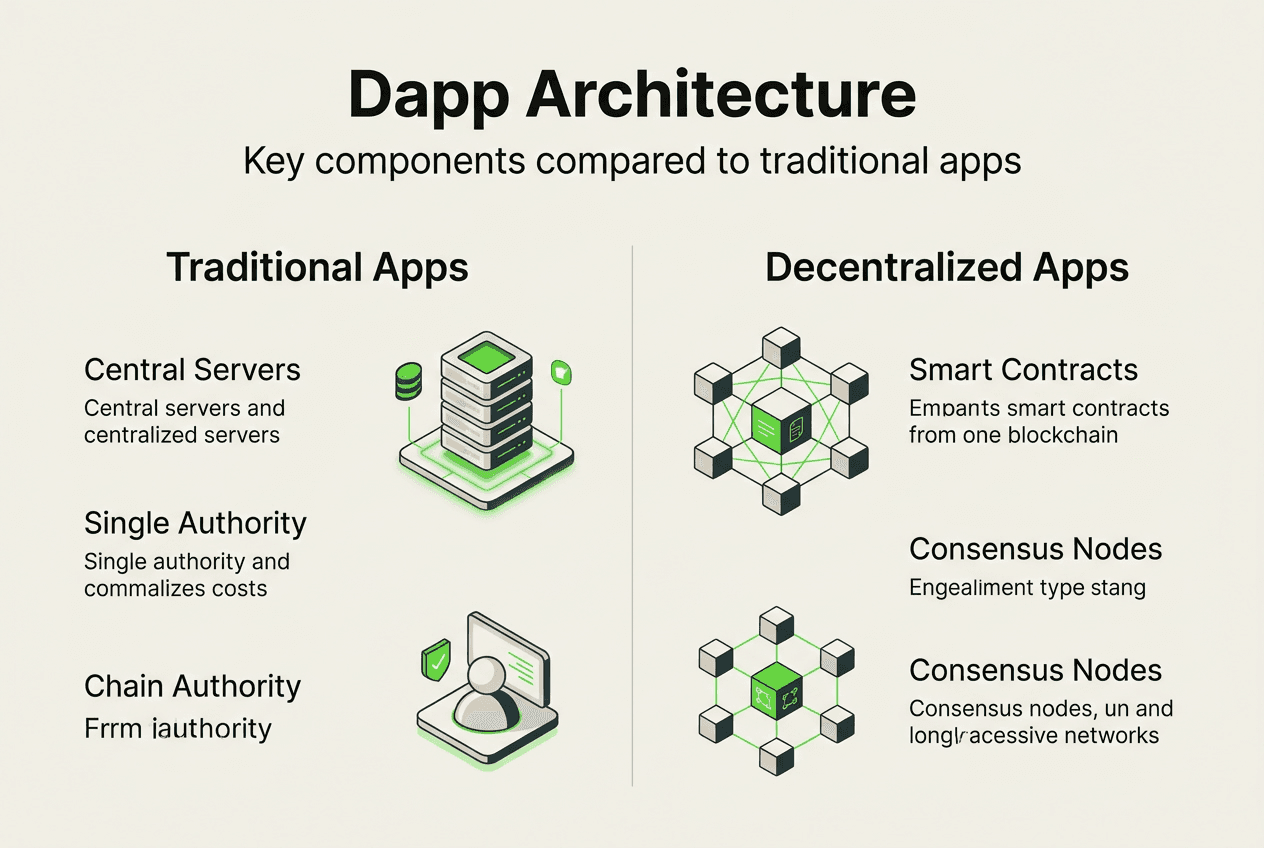
Key components and architecture of decentralized apps
Smart contracts form the immutable backend logic of decentralized applications, containing all business rules and data processing functions that execute automatically when triggered. Once deployed on the blockchain, the network as a whole will always be able to serve clients looking to interact with the contract, ensuring continuous availability even if individual nodes go offline. These contracts handle everything from token transfers to complex multi-party agreements, processing transactions according to predefined conditions without requiring manual intervention or trusted intermediaries.

Frontend interfaces provide the user experience layer, typically built with standard web technologies like JavaScript, React, or Vue.js. These interfaces connect to smart contracts through libraries such as Web3.js or Ethers.js, translating user actions into blockchain transactions and displaying results in familiar formats. The frontend can be hosted on traditional servers or decentralized storage systems like IPFS, giving developers flexibility in deployment strategies. Users interact with these interfaces through wallet applications that manage private keys and sign transactions, creating a seamless bridge between conventional user experiences and blockchain functionality.
Decentralized network consensus ensures that all nodes agree on the current application state without requiring a central authority to validate transactions. Validators or miners process new transactions, bundle them into blocks, and propagate these blocks across the network where other nodes verify their validity. This distributed validation creates resilience against attacks and failures, as compromising the system would require controlling a majority of network participants rather than breaching a single server.
| Component | Traditional Apps | Decentralized Apps |
|---|---|---|
| Backend Logic | Centralized servers controlled by company | Smart contracts on distributed blockchain |
| Data Storage | Company databases with single point of control | Distributed ledger across thousands of nodes |
| Availability | Depends on company infrastructure and operations | Network consensus ensures continuous operation |
| Code Updates | Deployed instantly by development team | Requires new contract deployment or governance vote |
| User Authentication | Username/password managed by company | Cryptographic wallet signatures controlled by users |
The blockchain infrastructure supporting dapps varies by platform, with Ethereum, Solana, Polygon, and other networks offering different tradeoffs in speed, cost, and decentralization. Each platform provides unique tools and capabilities that influence how you architect your application, from transaction throughput to smart contract languages and consensus mechanisms.
Common security challenges and risks in dapp development
Smart contracts are immutable once deployed, and flaws can be exploited by hackers who identify vulnerabilities in the permanent code. This immutability creates a double-edged sword where bugs cannot be patched through traditional software updates, requiring developers to deploy entirely new contracts and migrate user data. In July 2023, hackers drained over $70 million from Curve Finance in a matter of hours due to a cross-contract reentrancy attack that exploited how multiple contracts interacted with each other.
Common attack vectors targeting smart contracts include:
- Reentrancy attacks where malicious contracts recursively call vulnerable functions before state updates complete
- Integer overflow and underflow that cause unexpected calculation results
- Access control failures that allow unauthorized users to execute privileged functions
- Front-running where attackers observe pending transactions and submit competing transactions with higher fees
- Logic errors in complex conditional statements that create unintended execution paths
Client-side attacks can be as damaging as backend compromises leading to drained wallets and stolen assets when attackers compromise the frontend interface. Phishing sites that mimic legitimate dapp interfaces trick users into approving malicious transactions, while man-in-the-middle attacks intercept communications between users and blockchain networks. Frontend vulnerabilities often receive less attention than smart contract security, yet they represent the primary interaction point where users connect wallets and sign transactions.
Pro Tip: Implement a multi-layered security approach that includes formal verification of critical contract functions, bug bounty programs to incentivize white-hat hackers, and real-time monitoring systems that detect unusual transaction patterns before significant damage occurs.
Securing both frontend and backend requires different strategies tailored to each layer's unique risks. Smart contracts benefit from extensive unit testing, integration testing with realistic scenarios, and professional security audits by firms specializing in blockchain vulnerabilities. Frontend security demands secure coding practices, content security policies that prevent script injection, and user education about verifying contract addresses before approving transactions. Testing should include adversarial scenarios where you actively try to break your own application, simulating the mindset of attackers seeking to exploit any weakness. The staking dapp security approach demonstrates how careful architecture and thorough testing create robust applications that protect user assets.
Understanding cross-contract reentrancy patterns helps developers recognize how seemingly isolated contracts can create vulnerabilities when they interact, emphasizing the importance of analyzing your entire application ecosystem rather than individual components in isolation.
Governance and human factors in decentralized applications
Human-driven processes like leadership and community engagement shape governance outcomes in dapps, revealing that pure code-based decision making often proves insufficient for complex scenarios. While smart contracts execute predetermined rules automatically, they cannot adapt to unforeseen circumstances or make nuanced judgments that require context and values. Governance models must balance the transparency and automation of algorithmic rules with the flexibility and wisdom of human input, creating hybrid systems that leverage both strengths.
Algorithmic governance alone may not suffice due to rigidity and unforeseen circumstances that demand judgment calls beyond simple rule execution. Emergency situations like critical bugs or economic attacks require rapid human coordination to protect user funds, while long-term strategic decisions about protocol upgrades benefit from diverse stakeholder perspectives. The challenge lies in implementing human governance without recreating the centralization problems that blockchain technology aims to solve.
Social norms and community dynamics significantly influence how governance actually functions in practice:
- Token holder voting can be dominated by large holders or insiders with disproportionate influence
- Voter apathy leads to low participation rates that undermine legitimacy of decisions
- Informal leadership structures emerge naturally even in supposedly flat organizations
- Communication channels and community culture shape which proposals gain traction
Risks of re-centralization emerge when human intervention concentrates power in small groups that make unilateral decisions affecting all users. Multisig wallets controlled by founding teams, admin keys that can pause contracts, and upgrade mechanisms that bypass community approval all represent potential centralization vectors. These tools serve legitimate purposes for security and maintenance, but they require transparent processes and checks on authority to prevent abuse.
Steps for implementing effective decentralized governance:
- Define clear decision-making processes that specify who can propose changes, how votes are counted, and what thresholds trigger implementation.
- Create transparent communication channels where stakeholders can discuss proposals, raise concerns, and coordinate responses to emerging issues.
- Implement time delays and safeguards that prevent hasty decisions while allowing rapid response to genuine emergencies.
- Distribute governance tokens widely to ensure diverse stakeholder representation rather than concentration among insiders.
- Document all governance decisions and their rationale to build institutional memory and accountability over time.
The dapp governance insights demonstrate how successful projects balance automation with human judgment, creating systems that remain decentralized in spirit while acknowledging the practical need for leadership and coordination.
Scalability, testing, and best practices for building successful dapps
Scalability planning must begin during initial architecture design rather than becoming an afterthought when user growth overwhelms your infrastructure. Blockchain networks have inherent throughput limitations based on block size, block time, and consensus mechanisms that constrain how many transactions they can process per second. Layer 2 solutions like rollups, sidechains, and state channels offer ways to increase capacity by processing transactions off the main chain while inheriting its security guarantees. Your application architecture should anticipate growth patterns and implement scaling strategies appropriate to expected user loads.
Many projects perform well on testnets but struggle in production due to network load, revealing the importance of realistic testing environments that simulate mainnet conditions. Testnets typically have lower activity levels, faster block times, and different validator sets compared to production networks, creating false confidence about performance. Gas price volatility on mainnet can make transactions prohibitively expensive during congestion, while network latency affects user experience in ways that testnet environments fail to replicate.
Best practices for robust dapp development:
- Conduct professional security audits before mainnet deployment to identify vulnerabilities that internal testing missed
- Design intuitive frontend experiences that guide users through transaction signing and wallet interactions without confusion
- Implement comprehensive error handling that provides clear feedback when transactions fail or require user action
- Monitor contract events and transaction patterns to detect anomalies that might indicate attacks or bugs
- Create detailed documentation that explains contract functionality, governance processes, and user workflows
Pro Tip: Build a staging environment that mirrors your production setup as closely as possible, including realistic data volumes and transaction patterns, to identify performance bottlenecks before they impact real users.
| Common Pitfalls | Best Practices |
|---|---|
| Deploying untested contracts to mainnet | Extensive testnet validation plus security audits |
| Ignoring gas optimization in contract code | Profile gas usage and optimize expensive operations |
| Poor error messages that confuse users | Clear feedback explaining transaction requirements |
| No upgrade path for fixing bugs | Proxy patterns or governance-controlled upgrades |
| Overlooking mobile user experience | Responsive design and mobile wallet integration |
The blockchain development services ecosystem provides specialized expertise in architecture decisions, security reviews, and performance optimization that accelerate development while avoiding common mistakes. Professional teams bring experience across multiple projects and platforms, recognizing patterns that lead to success or failure. Tokenization and dapps services demonstrate how thoughtful design creates applications that scale efficiently while maintaining security and usability standards that users expect from production systems.
Explore expert blockchain development services
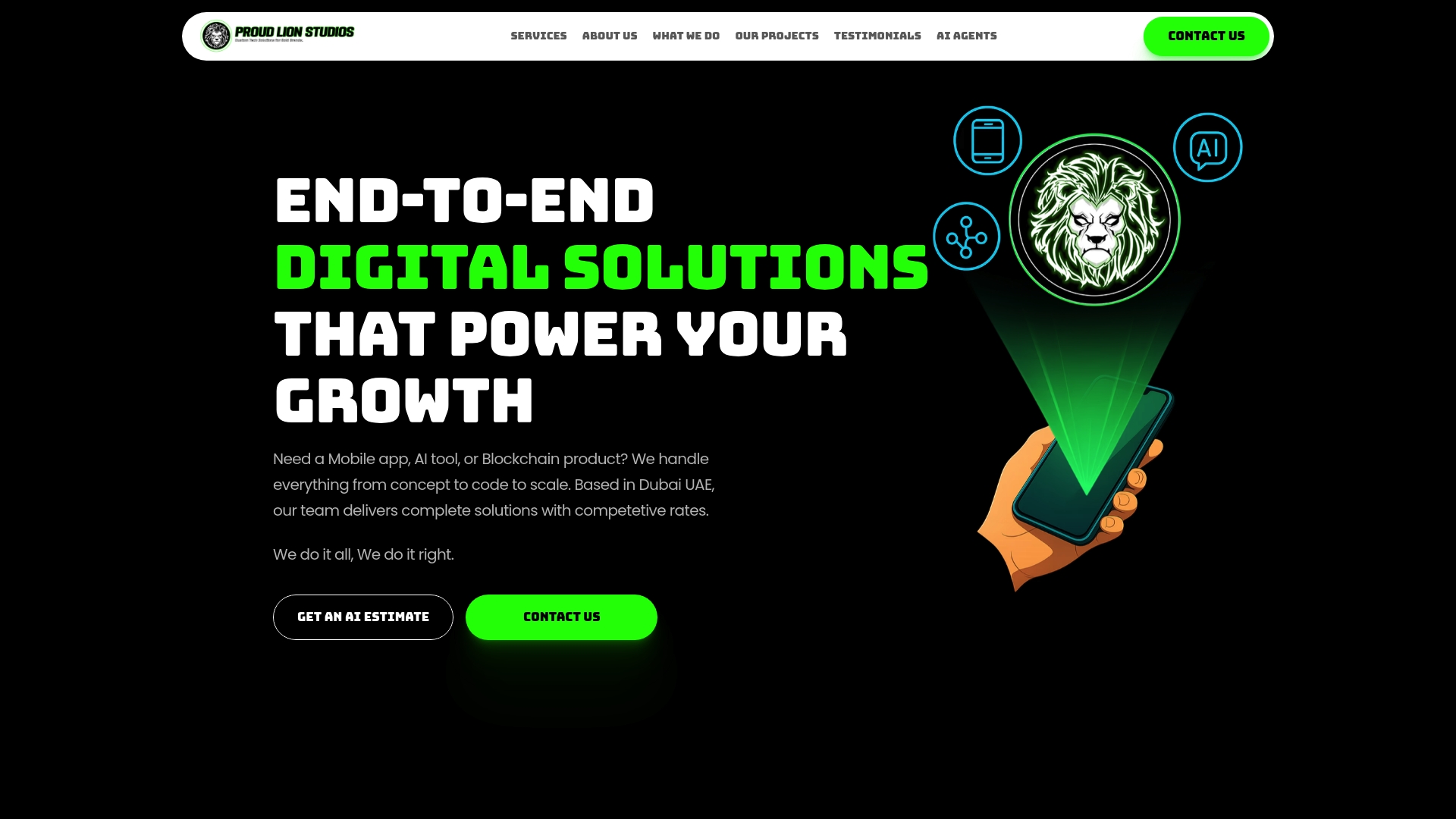
Building secure and scalable decentralized applications requires specialized expertise in smart contract development, blockchain architecture, and security best practices that most development teams lack internally. Proud Lion Studios offers comprehensive blockchain development services that transform your concept into production-ready applications built on proven patterns and industry-leading security standards. Our team specializes in smart contract development across multiple blockchain platforms, ensuring your backend logic executes flawlessly while protecting user assets from common vulnerabilities. We provide end-to-end tokenization and dapp implementation services that handle everything from initial architecture design through mainnet deployment and ongoing optimization. Partner with experienced blockchain developers who understand the nuanced challenges of decentralized systems and can guide you past the pitfalls that derail projects.
Frequently asked questions
What programming languages are used to build dapps?
Solidity dominates Ethereum smart contract development, offering a JavaScript-like syntax specifically designed for writing blockchain logic. Frontend interfaces typically use JavaScript or TypeScript with libraries like Web3.js or Ethers.js to connect to blockchain networks. Alternative blockchains support different languages: Rust for Solana and Polkadot, Vyper as a Python-like alternative to Solidity, and Go for building custom blockchain infrastructure.
How do dapps handle user data differently from traditional apps?
User data in dapps lives on the blockchain rather than centralized servers, creating permanent records that anyone can verify and audit. Users control their data through private keys rather than trusting companies to manage accounts and passwords. This immutability means you cannot delete or modify historical records, requiring careful consideration of what information gets stored on-chain versus off-chain storage solutions.
What are best practices to secure decentralized applications?
Conduct thorough smart contract audits by professional security firms before deploying to mainnet, identifying vulnerabilities that internal testing overlooks. Secure frontend interfaces against phishing attacks, script injection, and man-in-the-middle exploits through content security policies and secure coding practices. Test extensively on testnets with realistic scenarios that simulate adversarial conditions, and implement monitoring systems that detect unusual activity patterns in production environments.
Recommended
- Build mobile apps with AI, blockchain & game tech in 2026 - Software & Web3 Development in Dubai | Proud Lion Studios
- Build mobile apps with AI, blockchain & game tech in 2026
- Mobile apps in tech: startup growth strategies for 2026 - Software & Web3 Development in Dubai | Proud Lion Studios
- Mobile apps in tech: startup growth strategies for 2026
- f01i.ai – AI Crypto Trading Bot Builder | No Commissions | Automated Trading